Keylogger Basics - Part 1
”Keyloggers are a form of spyware that records user keystrokes. They can be either hardware devices or software programs. They record every key typed on a computer, sending this information to the person who installed it or saving it to be read later.The software versions may be delivered by Trojan horse email attachments or installed directly to the PC. The hardware version must be physically installed on the target machine, usually without the user’s knowledge. Although keyloggers are sometimes used in the payloads of viruses, they are more commonly delivered by a trojan-horse program or remote administration trojan (RAT)."
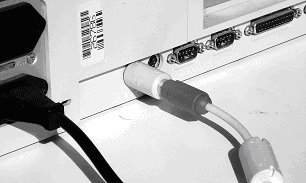
“Some hardware keystroke loggers consist of a small AA battery-sized plug that connects between the victim's keyboard and computer. The device collects each keystroke as it is typed and saves it as a text file on its own tiny hard drive. Later, the keystroke logger owner returns, removes the device, and downloads and reads the keystroke information. These devices have memory capacities between 8KB and 2MB, which, according to manufacturer's claims, is enough memory to capture a year's worth of typing.”
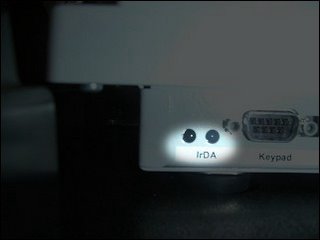
“The only way to detect hardware keyloggers is through physical inspection. Because the device resembles an ordinary keyboard plug, it’s easy for the victim to overlook. The fact that most workstation keyboards plug into the back of the computer makes them even harder to detect.”
Stay tuned for Part 2 of Keylogging Basics ...